Cybersecurity Hearing: The Grid is a Primary Target

House Cybersecurity Hearing “Keeping The Lights On: Addressing Cyber Threats To The Grid.”
On Friday, July 12, 2019, the House Subcommittee on Energy (Committee on Energy and Commerce) held a cybersecurity hearing entitled “Keeping The Lights On: Addressing Cyber Threats To The Grid.”
“Our Nation’s energy infrastructure has become a primary target for hostile cyber actors, both state-sponsored and non-state sponsored. The frequency, scale, and sophistication of cyber threats continue to increase. Cyber incidents have the potential to disrupt energy services, damage highly specialized equipment, and even threaten human health and safety.” – Assistant Secretary Karen S. Evans
There was a lot discussed and questions on several issues related to both electric grid and pipeline security. I would characterize the hearing as generally great questions from Congress – and a lot of non-answers and bureaucratic mouth-jive from FERC and NERC. The best answers came from DOE’s Karen Evans – but I wasn’t satisfied that DOE and DHS (who did not have a witness in the hearing) are moving quickly enough to protect the grid.
FERC and NERC Lack a Sense of Urgency
It was clear to me that FERC and NERC are making dangerously little progress. Here is one example (and there are many):
I reported that at a February 14, 2019 Senate hearing, NERC CEO James Robb looked like a deer in the headlights when Senator Angus King (ME) asked him if any of our utilities have Kaspersky, Huawei, or ZTE equipment or software in their systems. Mr. Robb not only didn’t know, but NERC hadn’t checked.
Fast forward to July 12, 2019 and NERC still does not know!! Mr. Robb hopes for an answer by “the end of the summer.”
Are you kidding me right now? There is a complete lack of urgency here.
Congresswoman Annie Kuster questions regulatory transparency
Ann Kuster (NH) raised concerns about the withholding of the names of CIP violators and the transparency of the regulatory system. This is an issue first uncovered by the Secure the Grid Coalition over a year ago and reported in detail HERE.
“I still have questions on how we can act in a more transparent way.” – Rep. Ann Kuster
Kudos to Congresswoman Kuster! This is the first time we have seen this issue raised in a Congressional hearing. Here is the clip of her questions – and very unsatisfying answers from Andy Dodge from FERC.
Hmmm. Let’s do a fact check here. I filed FOIAs in December 2018 and January 2019 for the names of 1,464 entities who violated CIP standards in 243 FERC dockets since July of 2010 (when the coverup began). Mr. Dodge claims that FERC has been going through the FOIAs and releasing names “as appropriate.”
Fact: As of the date of this hearing (July 12, 2019), FERC has released only 4 out of the 1,464 requested names and denied 3 others. They had only processed 7 dockets out of 243. At this rate, it will take FERC 17 years to process my FOIAs. (See the details on my FOIAs and FERC’s responses HERE.)
I’d say Mr. Dodge was not very transparent in his answer to Congresswoman Kuster.
What would a disruption mean for citizens? Apparently, Nothing.
One of the best questions – with the scariest lack of answers – was from Representative Marc Veasey (TX). His question was “what a disruption to an electrical distribution network or a natural gas pipeline would mean to citizens.” FERC didn’t know. NERC said a disruption would likely be contained locally and would not cascade.
Huh?
So FERC and NERC – we citizens have nothing to worry about? There will be no cascading outage in a cyberattack and nobody will die? This complete downplaying of the threat and unacceptable answers to Representative Veasey’s excellent question was very disturbing.
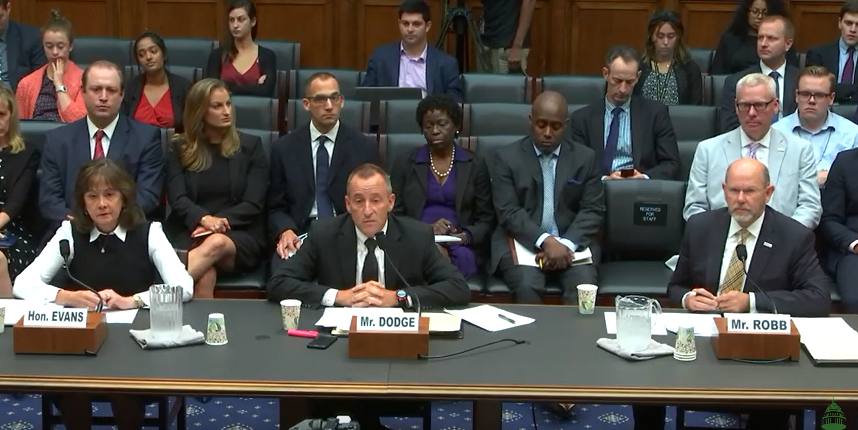
Witnesses:
The Honorable Karen S. Evans
Assistant Secretary Office of Cybersecurity, Energy Security, and Emergency Response (CESER)
U.S. Department of Energy
J. Andrew (Andy) Dodge, Sr.
Director Office of Electric Reliability
Federal Energy Regulatory Commission
Mr. Jim Robb
President and Chief Executive Officer
North American Electric Reliability Corporation
You can watch the whole House cybersecurity hearing here: